Next-Generation Endpoint Detection and Response
Advanced threat detection, 24/7 expert monitoring, and flexible deployment options — designed to protect your organisation wherever it operates.
How HexaFort EDR Works
HexaFort EDR is an advanced endpoint security solution that continuously monitors servers and workstations for suspicious activity. By combining behavioural analytics with machine learning, it detects threats that traditional antivirus and endpoint protection platforms (EPP) often miss — from ransomware and fileless malware to targeted attacks and insider threats.
Our lightweight agent installs on your endpoints, collecting telemetry on processes, network connections, file system changes, and user behaviour. This data is analysed in real time, and when a potential threat is identified, our platform can automatically isolate the affected endpoint, terminate malicious processes, or alert your security team with detailed forensic context.
Core Capabilities
24/7 Monitoring and Response
Whether you choose our fully managed Cloud service or deploy On-Premise, your endpoints are continuously monitored. In our managed model, a dedicated team of security analysts works around the clock to detect, investigate, and respond to incidents — giving you peace of mind without expanding your internal headcount.
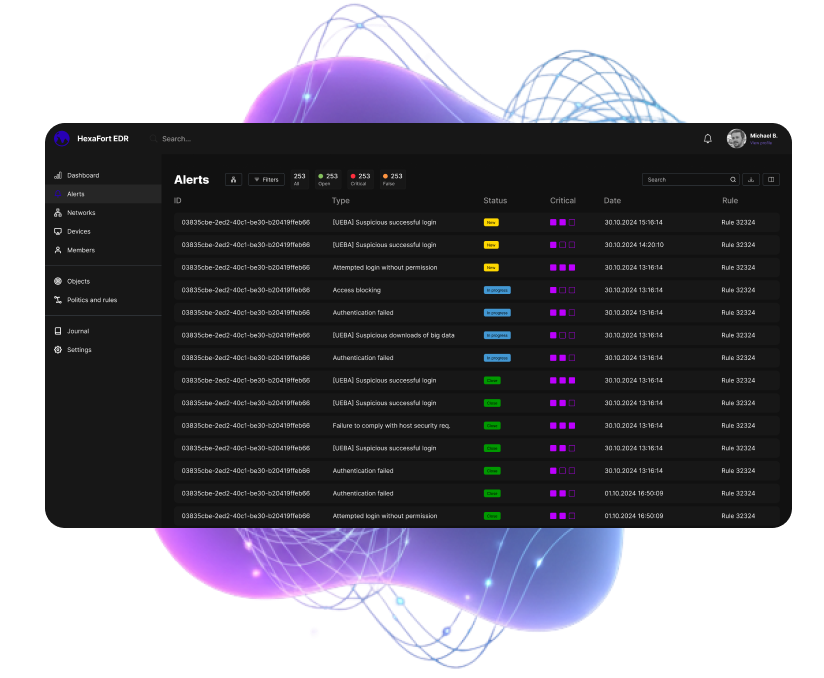
Detection of Advanced Threats
HexaFort EDR goes beyond signature-based detection. Using behavioural analysis and user and entity behaviour analytics (UEBA), we identify:
- Ransomware and fileless malware
- Living-off-the-land (LotL) attacks that abuse legitimate system tools
- Advanced persistent threats (APTs) that hide for months
- Compromised accounts and insider threats
- Zero-day exploits and previously unknown malware
Rapid Incident Investigation
When an alert is triggered, our platform provides a complete timeline of events — from initial compromise to lateral movement. Security analysts can drill down into process trees, network connections, and file changes to understand exactly how an attack unfolded and which systems were affected.
Automated and Manual Response
Respond to threats at machine speed. Define custom playbooks to automatically contain threats — isolating endpoints, blocking network connections, or rolling back malicious changes. For complex incidents, your team can use our forensic tools to perform manual remediation.
Policy Enforcement and Compliance
Ensure your organisation adheres to internal security policies and regulatory requirements. HexaFort EDR allows you to define rules for allowed applications, devices, and network destinations, alerting on violations and preventing unauthorised activities.
Deployment Options
We understand that every organisation has unique requirements. That’s why HexaFort EDR is available in two flexible deployment models.
Cloud Service (SaaS)
The fastest path to enterprise-grade endpoint security.
Ideal for — organisations without an in-house SOC, distributed teams, or those seeking to optimise security costs
Fully managed — our global security operations centre (SOC) handles monitoring, detection, and response 24/7
No infrastructure to maintain — the platform is hosted and managed by HexaFort
Automatic updates — threat intelligence, detection rules, and software updates are delivered continuously
Predictable subscription pricing — pay per user per year with no upfront capital expenditure
On-Premise Service
Complete control for organisations with specific data sovereignty or customisation needs.
Ideal for — enterprises with mature security teams, strict compliance mandates, or air-gapped environments
Full data residency — all telemetry and logs remain within your own infrastructure
Seamless integration — connect with your existing SIEM, SOAR, and ticketing systems
Custom configurations — tailor detection rules, response playbooks, and reporting to your exact requirements
Optional SOC augmentation — add our expert team to assist with complex investigations or overflow alert triage
Why Organisations Choose HexaFort EDR
Global Expertise, Local Support
Our analysts are distributed across multiple time zones, ensuring round-the-clock coverage for clients in the UK, Europe, Asia, and the Americas. We provide support in English and work with you to align with your business hours and incident response processes.
Cost‑Effective Protection
We believe enterprise-grade security should be accessible. Our transparent pricing model — starting at £35 per user per year for the Cloud service — includes all core capabilities, with no hidden fees for updates, threat intelligence, or basic support.
Vendor‑Neutral Approach
HexaFort EDR integrates with the tools you already use. Whether you rely on Splunk, QRadar, or an open-source SIEM, our open APIs and pre-built connectors make integration straightforward. We don’t force you to adopt a full ecosystem — you choose what works for your organisation.
Reduced Operational Burden
Our managed Cloud service removes the need to build and maintain an in-house security operations centre. Your internal team is freed from routine monitoring and alert triage, allowing them to focus on strategic security initiatives, risk management, and business enablement.
Threat Coverage at a Glance
| Threat Type | How HexaFort EDR Protects You |
|---|---|
| Ransomware | Behavioural analysis detects encryption anomalies and automatically isolates affected endpoints before the attack spreads. |
| Fileless Malware | Memory-level monitoring and tracking of system utilities (PowerShell, WMI, PSExec) identifies attacks that leave no traces on disk. |
| Advanced Persistent Threats (APTs) | Continuous telemetry collection and long-term retention enable retrospective analysis to uncover stealthy, long‑term compromises. |
| Compromised Accounts | UEBA establishes normal user behaviour patterns and flags suspicious login times, unusual data access, or atypical command execution. |
| Insider Threats | Monitor and control data transfers, unauthorised device connections, and access to critical systems — with alerts for policy violations. |
| Zero‑Day Exploits | Machine learning and heuristic analysis detect anomalous activity without requiring prior knowledge of the threat. |
| Policy Violations | Define application whitelists, USB device controls, and network restrictions to prevent non‑compliant activity before it becomes a risk. |
Get Started with HexaFort EDR
We offer personalised consultations and pilot programmes to help you evaluate HexaFort EDR in your own environment.
